PC security: How to protect computers and yourself from hackers, ransomware, viruses, Trojans, malware, phishing and investment scams, etc.
This section of this website consists of several pages, listed under CONTENTS below, that deal in-depth with PC security.
By reading this article all the way through, you will be provided with all of the information you need to keep your personal information and your desktop and laptop computers secure.
The criminal hackers who are after your personal details, website user names, passwords, etc., in order to be able to help themselves to your money or use your accounts, are having to develop ever-more ingenious ways of fooling users into providing them. Therefore, PC security is something that all computer users who go online have to keep themselves constantly informed of – that is, of the latest developments with regard to both the latest protective measures and the latest criminal tricks being employed.
HTTPS Everywhere
HTTPS at the beginning of a particular website’s pages in the address bar instead of just HTTP means that secure encryption is active protecting the connection between the user’s computer and the website’s server.For example, this is the home page of this website – https://www.pcbuyerbeware.co.uk/. It has an https security certificate,
If you add HTTPS Everywhere as an Add-on to a web browser (Firefox, Chrome, Opera), it makes sure that you can only access secure websites that use HTTPS. Hackers and cyber criminals, who spoof a website, will not be able to obtain a security certificate that provides a secure https connection. Therefore, with the Add-on enabled, your web browser won’t allow you to use an insecure http website that may be spoofing a genuine https website. All banks, store and payment websites, such as Amazon and PayPal use https connections. Find out more about HTTPS Everywhere from the following website:
HTTPS Everywhere – https://www.eff.org/https-everywhere
Ransomware
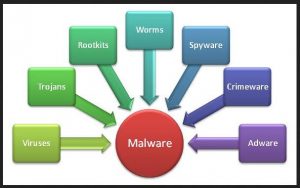
The latest developing threat is dangerous malware called Ransomware.
The following post fills in the details. –
How to avoid and deal with the ever-growing threat of ransomware –
https://www.pcbuyerbeware.co.uk/blog/avoid-remove-ransomware-infections/
Intel processors getting security updates
Processors do get microcode updates that fix operational and security bugs.
Intel CPUs Are Getting Mystery “Critical” Security Updates [January 2022] –
https://www.howtogeek.com/781308/intel-cpu-are-getting-mystery-critical-security-updates/
Free check of your email accounts for data breaches
Cold calling has fallen out of favour with cybercriminals. Most scams are delivered by email. You can check your email accounts free of charge for data breaches by using the service that Malwarebytes, a major security-software developer, provides.
CHECK YOUR ACCOUNTS FOR BREACHES –
https://www.malwarebytes.com/hibp
CONTENTS
1.- This page: Introduction to online and offline PC security
2. – The great dangers presented by identity theft
3. – Tips on how best to remain secure online
4. – What to do If you allow malware to install itself
5. – Protection against malware
6. – System encryption software
7. – The Action Center in Windows 7 & 8.1 is called Security and Maintenance in Windows 10
8. – The essential security-protection methods
PC SECURITY-RELATED POSTS ON THIS WEBSITE
POST: Bitdefender internet security products 2023
POST: Browser fingerprinting tracking by websites and their advertisers
POST: Windows 10/11 Print Spooler security problems
POST: iPhone VPN – Should my iPhone use a VPN?
POST: VPNs – the essential features
POST: Bitdefender review – The best Internet security software currently available
POST: Smart TV Snooping – Automatic Content Recognition (ACR) – How to turn it off
POST: How to use the DNS Over HTTPS (DoH) protocol to improve online security
POST: Fraudbusters – How victims of large online scams can get their money back if the banks refuse compensation
POST: Explaining the smishing (SMS phishing), vishing and SIM card swap and theft scams
POST: Opera, a fast, secure, easy-to-use web browser that provides a free VPN and ad blocker
POST: Equifax hacked – The implications of the massive hacking of the Equifax credit reference agency
POST: Does using a Virtual Private Network (VPN) protect your privacy from hackers and legal invasions such as the UK Snoopers Charter?
POST: Password recovery – Recover or reset passwords for Windows – OS X – iOS – Android and Linux devices
POST: Face recognition – Facebook and Google want to identify you in images
POST: Cyber criminals and hackers use Facebook to obtain personal information
POST: How to avoid and deal with the ever-growing threat of ransomware
POST: Samsung updates – Does Samsung update all of its Android phones and tablets to the latest version?
POST: Cyber criminals and hackers use Facebook to obtain personal information
POST: Protect yourself when using public unsecured wireless networks
POST: Protect computers from crooked PC repair companies
POST: Malware PUP that can replace a web browser with a fake copy
POST: Many Google Android devices are easily hacked
POST: Phony Critical Firefox update message that presents itself automatically as a webpage
Computer and online security-related articles on the web
1, – New device? Here’s how to safely dispose of your old one –
On Windows, Apple, Android devices and Chromebooks.
2. – Why scanning QR codes can be a security risk on a par with clicking unknown links in emails – https://www.youtube.com/watch?v=QQBNdTNlTHg
3. – How to keep your apps up to date in Windows 10 and 11 –
Out-of-date apps can allow hackers to gain entry into a computer and its network. Even the Windows Print Spooler that all versions of Windows use brought about serious system vulnerabilities.
4. – What Are Decentralized VPNs? – [August 2021] – Virtual Private Networks provide security by using encryption making it look as if your web connection is coming from an IP address in a foreign country –
https://www.howtogeek.com/741691/what-are-decentralized-vpns/
5. – Can My ISP See If I’m Using a VPN, and Do They Care? –
https://www.howtogeek.com/749839/can-my-isp-see-if-im-using-a-vpn-and-do-they-care/
6. – Fake parcel delivery texts are the top text scam with con representing over half of all smishing attempts: We reveal how you can protect yourself [August 2021] –
https://www.dailymail.co.uk/money/beatthescammers/article-9897637…
7. – The one reason your iPhone needs a VPN –
https://blog.malwarebytes.com/privacy-2/2021/03/the-one-reason-your-iphone-needs-a-vpn/
8. – What to do if you’re the victim of a bank-transfer Authorised Push Payment (APP) scam [March 2021] –
9. – Why Data Privacy Day matters: A Lock and Code special with Mozilla, DuckDuckGo, and EFF –
https://blog.malwarebytes.com/podcast/2021/01/data-privacy-day-lock-and-code-special/
10. – Investment and pension scams during coronavirus lockdown – how to stay safe [April, 2020] –
https://www.hl.co.uk/news/articles/investment-and-pension-scams-during-coronavirus-lockdown…
11. – Scam call warning: Amazon Prime ‘renewal’ [13 February 2020] –
https://conversation.which.co.uk/money/amazon-prime-renewal-scam-phone-call/
12. – How to Detect Hidden Surveillance Cameras With Your Phone ]April, 2019] –
https://www.howtogeek.com/411095/how-to-detect-hidden-surveillance-cameras-with-your-phone/
13. – Best Chrome VPN extension 2019: Secure your browsing and access geoblocked content [June, 2019] –
https://www.expertreviews.co.uk/vpns/1409181/best-chrome-vpn
14. – UK Phone companies to end bank text scams – [December, 2018] –
https://www.which.co.uk/news/2018/12/phone-companies-to-end-bank-text-scams/
The video below is a discussion with a router expert from router-manufacturer Asus lasting 2 hours 20 minutes. Modern routers can provide security features when enabled, such as blocking malicious or hacked websites.
Introduction to online and offline PC security
TIP – Malware scanners: I have installed Avast Free Antivirus on several computers and use it myself. The free versions of Avira and Bitdefender are good. Note that only the paid-for versions provide protection against ransomware.
Only ever trust security warnings that are produced from the System Tray/ Notification Area in Windows. Even if a security warning seems to be produced outside that area by the anti-virus program that you use, don’t click on any message that comes up, not even a Cancel button, shut the web browser down immediately by pressing the Ctrl+Alt+Del key combination that provides access to or brings up the Windows Task Manager, which allows you to terminate any running program.
Hackers know that many people use the free malware (malicious software) scanners so if they create a message or presentation that seems to have been produced by the one they use, they will trust it and initiate a fake system scan that delivers real malware. It’s also good insurance to create a master image of your system on a regular basis, which the Backup and Restore tool in Windows 7/8.1/10 can all do, and save it to an external hard disk drive that you should keep disconnected from your computer to protect it from a virus infection and in case of destructive electrical spikes or lightning strikes.
For the backup and imaging provided by Windows 8.1 and 10 be aware that Microsoft wants out of taking business from the backup companies and so made the backup feature in Windows 8.0/10, which is the same as Windows 7, difficult to find.
Visit Backup Methods: How to Make Restorable Backups and System Images on this website for detailed information about how to create backups and use online storage services.
If you apply the PC security measures provided on the pages of this article, you shouldn’t experience any security-related problems, and, if you do, you’ll know how to fix them.
All computers that go online must be kept fully updated
It is imperative that you keep any kind of computer running Windows (or any other operating system) fully updated with the latest security updates. When run, the Belarc Advisor, under FREE DOWNLOAD on belarc.com, tells you if your computer has all of the available updates installed. It also provides a System Security Status report that gives your computer a security rating out of 10, created by the benchmark tests of the Center for Internet Security (CIS), which is at cisecurity.org.
It is far more risky accessing banking and log-on sites using a mobile smartphone or tablet than a standard PC
Smartphones and tablets are now small mobile personal computers that can be infected by virus and other malware infections in the same ways as desktop and laptop PCs. You can be caught out by scams or infected by malware when using a smartphone in exactly the same ways as any other computer usage.
Google’s Android is now the most commonly used smartphone operating system that is now being targeted by cyber criminals. Google also logs all of the information that your phone company logs via its Android operating system and uses the information and information it has gathered on you from your use of its services to serve you with customised ads. I personally find that an unacceptable invasion of my privacy, so I only use a standard mobile phone that can’t access the web. If I had to buy a smartphone, I would get an iPhone or a Windows phone, because with those only your phone company logs your calls and web browsing history.
I personally would never use a smartphone to access bank accounts, PayPal, Amazon or any other website that holds data on you, such as your credit card number. Some smartphones have found to be pre-installed with fake apps such as faked Netflix apps. I only do that from a home computer connected to the web with a wired, not a wireless connection, with private browsing enabled – all of the main browsers provide it and it has to be enabled every time you open the browser – and my router’s hardware firewall enabled.
Better still, only access banking websites using a Linux boot disc. If you download the Ubuntu Linux ISO-file installation file, for example, it can boot a PC from a DVD disc it is burned to as if it were installed and access the web using its Firefox browser. Remember that the PC’s BIOS has to be set to boot first from the DVD drive to boot from a disc. If no disc is detected it boots from the next device in the boot order, usually the hard drive.
Most web connections are now provided by a wireless router around which a home network, which could consist of wireless and wired computers – desktops, laptops, tablets and smartphones – are connected.
Malwarebytes for Android – “Aggressive detection of adware and potentially unwanted programs keeps your Android phone or tablet running smooth. A privacy audit tells you which apps are monitoring your every move. All that protection in a lean package.” –
https://www.malwarebytes.com/mobile/