About the Meltdown/Spectre Intel & AMD processor flaws that give rise to security vulnerabilities that can be exploited by cyber criminals and hackers
According to their manufacturers, hardware flaws in Intel and AMD processors render them vulnerable to the critical Meltdown/Spectre security vulnerabilities discovered in January 2018, which can be exploited by hackers and cyber criminals. Apparently, the Meltdown flaw, which does not affect AMD processors, can be fixed by software updates and to some extent they can also fix the Spectre flaw. However, the most critical Spectre flaw will only be completely fixed by a redesign of processors made by Intel, AMD and ARM.
AMD processors are not vulnerable to the Meltdown flaw
Note that AMD processors are NOT vulnerable to the Meltdown flaw, only to the the more critical Spectre flaw. Intel processors are vulnerable to both flaws.
Indeed, AMD processors are very much less affected by the Spectre flaw than Intel’s processors. AMD has stated that, due to their architectures, its processors have a “near zero” performance slowdown that affects Intel processors when patches are installed. Moreover, AMD has stated that installing the patches is optional, not essential. In other words, only Intel’s processors are critically affected by both the Meltdown and Spectre flaws.
Unfortunately, Intel and Microsoft are only catering to the vulnerabilities in relatively recent Intel processors and, in Microsoft’s case, only to Windows 7/8.1/10, not Windows XP/Vista. Apparently, AMD and Microsoft intend to fix the Spectre flaw in old and recent AMD processors.
KB4090007: Intel microcode updates [Spectre security vulnerability]
Applies to: Windows 10 version 1709 – Windows Server, version 1709 (Datacenter, Standard)
https://support.microsoft.com/en-us/help/4090007/intel-microcode-updates
Windows operating system security update for AMD-based devices –
“Microsoft worked with AMD to resolve update blocks on a small subset of older AMD processors (that were previously blocked to avoid users getting into an unbootable state after installation of recent Windows operating system security updates).” – The security updates to Windows 7/8.1/10 were blocked from installing and creating an unbootable state.
https://support.microsoft.com/en-us/help/4073707/…
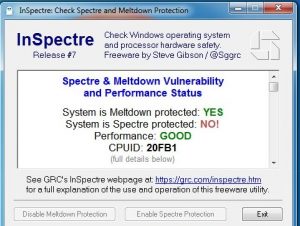
The image, at the top of this page, shows the result when the InSpectre tool, a development of the Gibson Research Corporation, was run (date: March 2018) on a PC running Windows 7, using an old Socket 939 AMD Athlon 64 X2 dual-core processor. As can be seen, it has no protection against its vulnerability to Spectre, but works perfectly well. This means that the system is only vulnerable to exploitation of the Spectre processor hardware-coding flaw by hackers and cyber criminals. All updates from Microsoft were installed before running the tool.
Updates to UEFI BIOS, operating system and even web browsers is required to fix the flaws
Apparently, to patch the Meltdown/Spectre flaws requires updates to the system BIOS or UEFI BIOS, the operating system (Windows, Linux, etc.) and even to the web browsers in use (Firefox, Opera, Edge, Safari, etc.) Most web browsers receive automatic updates from their developers. Note, however, that most browsers no longer provide updates for Windows XP/Vista, which Microsoft no longer supports. So, if you are still using them – they can be used as usual and to go online – they will slowly get less and less effective as the web moves on and malware scanners abandon them. For your information, I still use Windows XP on my dual-boot WinXP/Win7 PC. You can’t get the AVG scanner to download to WinXP, but AVG is currently (March 2018) updating AVG on its installation of WinXP. Who know for how much longer?
How to Check if Your PC or Phone Is Protected Against Meltdown/Spectre –
https://www.howtogeek.com/338801/how-to-check-if-your-pc-is-protected-against-meltdown-and-spectre/
According to the Gibson Research Corporation, “Protection from these two significant vulnerabilities requires updates to every system’s hardware – its BIOS which reloads updated processor firmware – and its operating system – to use the new processor features. To further complicate matters, newer processors contain features to minimize the performance impact of these important security improvements. But older processors, lacking these newer features, will be significantly burdened and system performance will suffer under some workloads.”
The text in red above, may indicate that these flaws could have been made issues on purpose in order to encourage users to update their hardware (processor/BIOS) and version of Windows. Moreover, only the older Intel and AMD processors suffer lower performance issues when the updates are installed.
Windows 7 is suffering the most from Microsoft’s security updates
Notice how Windows 7 is suffering the most from Microsoft’s security updates that deal with these flaws.
For example, Win7 systems can be rendered incompatible with their antivirus software and cause blue-screen-of-death errors. Win7, introduced in 2009, is still stubbornly a very popular version of Windows. According to StatCounter, in February 2018, 41.55% of desktop and laptop PCs were using Win7 compared to 43.54% using Windows 10. So you can see why Microsoft wants to get rid of Win7 that only loses its support in 2020.
Old PCs that use the old BIOS are never going to be able to obtain a BIOS update. The new UEFI BIOS was introduced at around the same time as Windows 7 in 2009, therefore only fairly recent systems will be able to obtain a UEFI BIOS update, simply because the older a PC’s motherboard is, the less likely that a UEFI BIOS update is available.
There is no BIOS update available for my old dual-boot Windows XP/Windows 7 desktop PC that runs an AMD Athon 64 X2 processor, therefore as long as it keeps working well, as it is, I intend to keep using it.
The InSpectre tool identifies if your PC has the critical Meltdown/Spectre security vulnerabilities
As shown in the image at the top of this page, the InSpectre tool from Gibson Research tells you if your system is vulnerable to the Meltdown/Spectre flaws. You just have to download, install and run it. Moreover, its download page provides plenty of useful information on the bugs.
InSpectre tool – https://www.grc.com/inspectre.htm
Microsoft blocks all Windows 7 security updates unless antivirus protection is present
Microsoft is now withholding security updates from Windows 7 users who don’t have antivirus software installed. A security patch that addresses the Meltdown and Spectre problems was installed by Windows Update. This brought about incompatibility issues with many antivirus tools, causing caused blue-screen-of-death errors.
Microsoft Blocks All Windows 7 Security Updates Unless You Have Antivirus –