A serious WordPress plugin vulnerability has led to the security of 100,000+ websites being compromised
A WordPress plugin vulnerability in a plugin called Slider Revolution or RevSlider that is bundled with many themes has led to 100,000+ websites being compromised. Therefore, if you have one or more WordPress sites make sure that they are updated.
RevShare develops the plugin and has fixed the problem with an update, but the WordPress community is mostly not aware of its existence.
What the vulnerability makes insecure
The vulnerability makes the wp-config.php file accessible, which gives access to the compromised site’s full database.
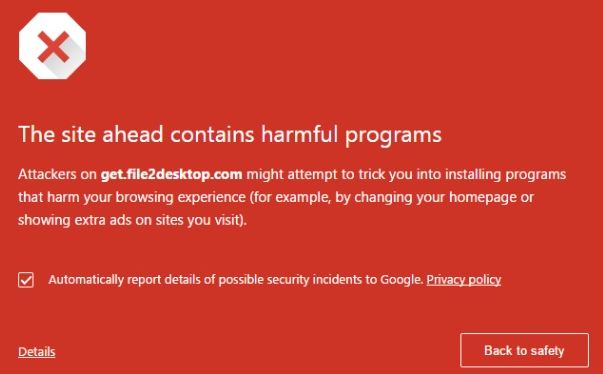
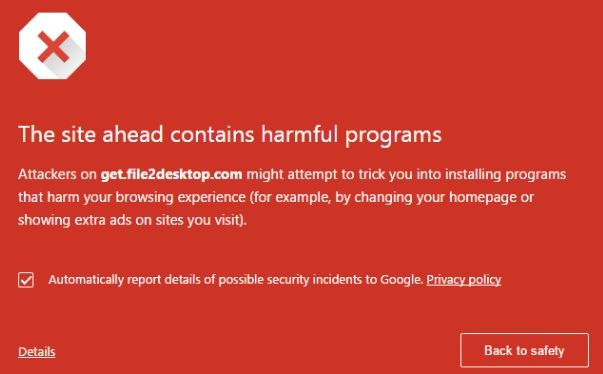
Google can detect if a site has the vulnerability and, in order to limit the damage that can be caused, has blocked them by providing visitors with an alert that says that an affected site is infected with malware.
A free website malware and security scanner
Click the link provided below if you want to use the “Free Website Malware and Security Scanner” provided by the security site, Sucuri.
Vulnerable plugins
Version 4.2.0 of the RevSlide plugin is required to be safe. ShowBiz Pro is another affected plugin. It requires version 1.5.3 or later. Below is a video on how to update the RevSlide plugin. The same method is used to update any other compromised WordPress plugin.
Revolution Slider Hacked – Upload Latest Version of Slider Revolution 4.5 –
Always use the latest version of WordPress itself and update plugins
It is always advisable to use the latest version of WordPress itself and update any plugins as soon as possible in order not to fall foul of existing vulnerabilities.
If the theme of your site or the version of WordPress no longer supports any plugins, you need a new plugin that carries out the same functions or you need a new theme.
The web provides free information on how to achieve almost everything in WordPress. Here is an example of an article on how to change a theme properly.
How to Properly Change a WordPress Theme (Ultimate Guide) –
https://www.wpbeginner.com/beginners-guide/how-to-properly-change-a-wordpress-theme/
However, note well that plugin and WordPress version updates can cripple an entire site or make parts of it fail, so always make sure that your plugins are 100% compatible with the latest version of WordPress before you update them or the version of WordPress. Also always create a restorable backup of your WordPress site before updating anything critical to it. I use the free version of UpdraftPlus Backup plugin.
There is nothing that can be done about vulnerabilities that have been identified by hackers but which have not been identified by the developers of plugins that are called zero-day exploits, because they cannot be fixed unless the developers are aware of them.